VCF on VCD: 2a – Certificates
I know, I wrote in my previous blog (https://my-sddc.net/creating-a-vcf-lab-on-top-of-vcd-part-2-workload-domain/) that the next steps would be related to networking and creating application, but there are a couple of housekeeping activities that need to be completed, before moving on. Therefore, this 2a blog, before I can deploy the networking components (and a 2b is to follow).
What we need to do are the following things:
- Configure certificates (2a)
- Configure backups (2b)
Configure Certicifates
By default all the components have a self-signed certificate installed. That might be fine for a home-lab and some companies still use this as well, but more and more organizations choose to configure certificates that are signed by a Certificate Authority within their own environment. And I think it is important to do that as well, to make sure that communication is safe.
The following steps will be taken to get to where we want to:
- Install the CA Roles (if you don’t already have a CA available)
- Change IIS Settings to allow Basic Authentication
- Create the user with the correct permissions to request a certificate
- Create the correct template (and publish it) with Microsoft CA
- Configure the CA settings in VCF
- Test
Install the CA Roles (if you don’t already have a CA available)
In order to do this, I have configured a Microsoft based CA, conform the default settings, on the DC01 that was already in my environment (added the following roles):
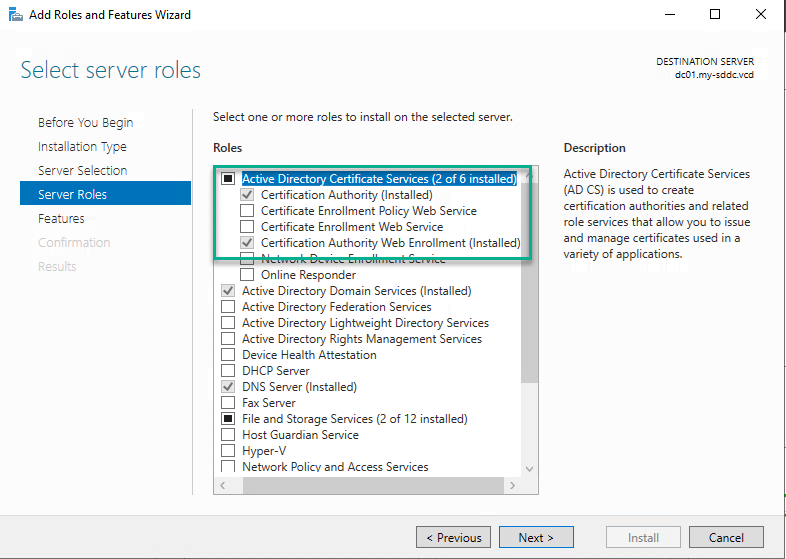
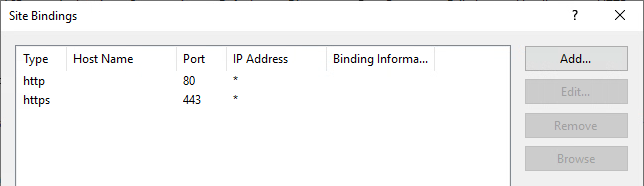
Also make sure the Web Server role is also installed, including the “Basic Authentication” option (under Security) ánd make sure that https is configured under “Site Bindings” (and the certificate used matches the name of the server):
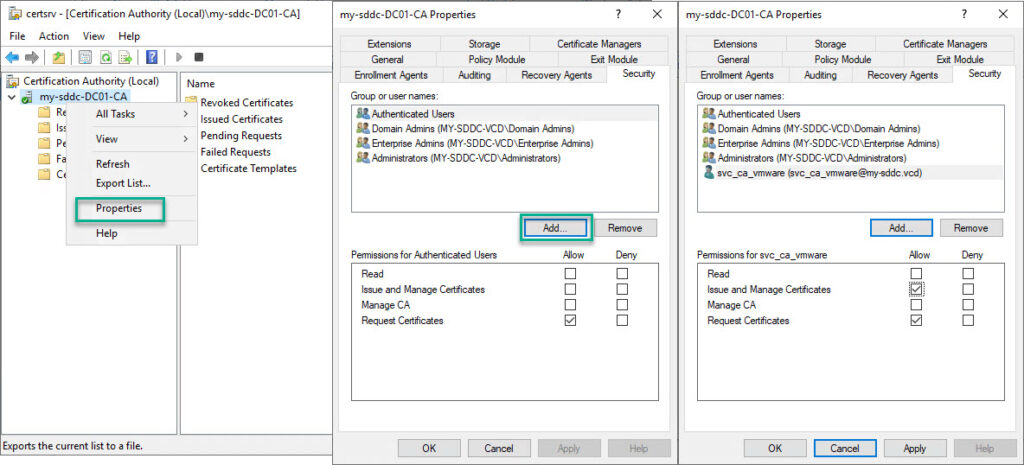
Create the user with the correct permissions to request a certificate
I have created an AD user, called svc_ca_vmware with the permissions to request a certificate (in certsrv.msc):
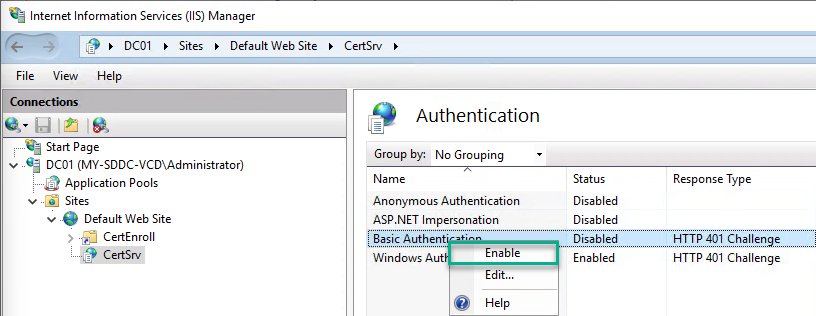
Change IIS Settings to allow Basic Authentication
Create the correct template (and publish it) with Microsoft CA
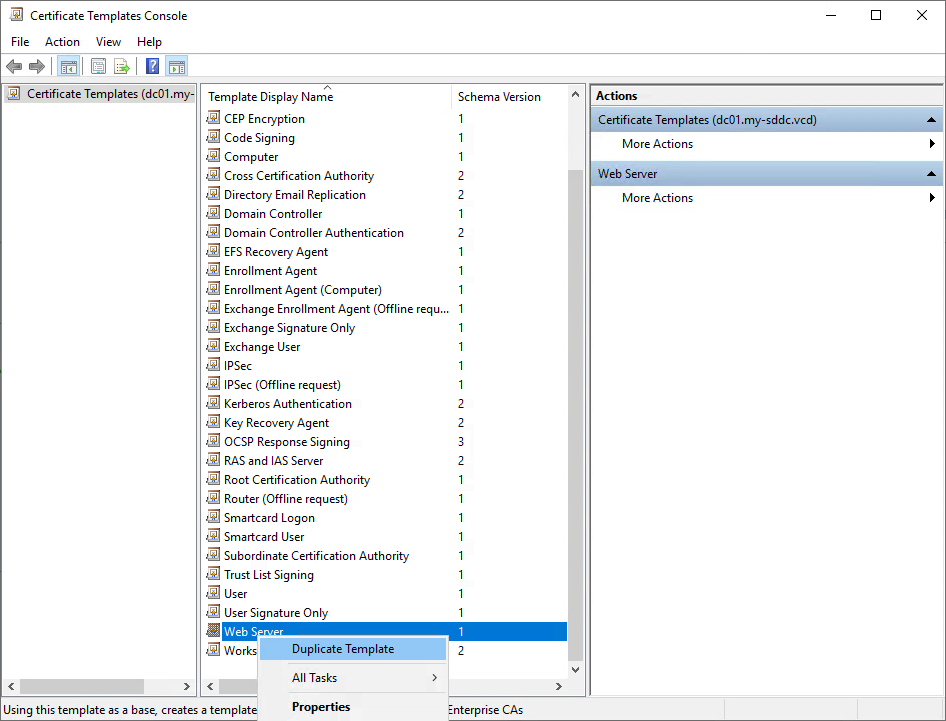
Then we can configure the correct Template, by making a copy of “Web Server” (in the “Certificate Template Console (certtmpl.msc)).
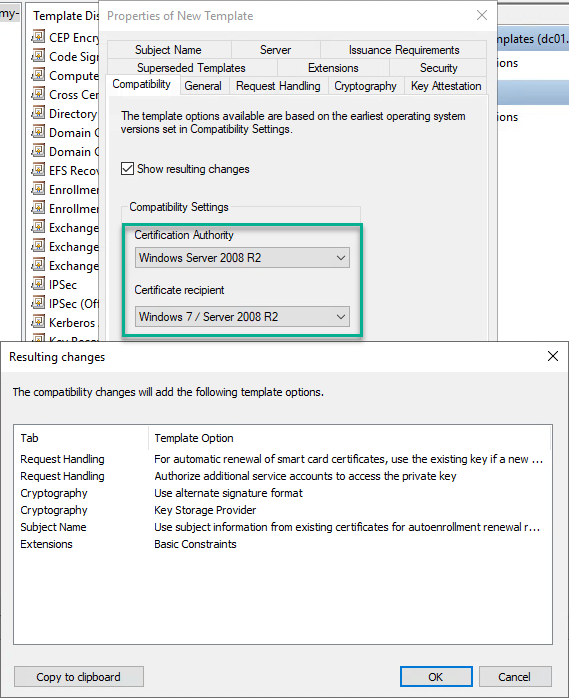
Change the Compatibility Settings:
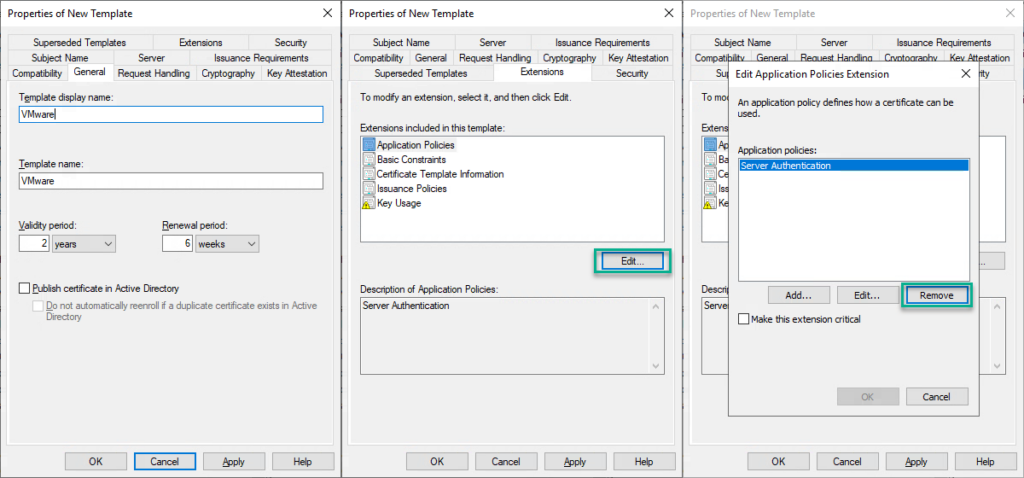
Give the new certificate a name, and remove”Server Authentication” as an “Application Policy Extension” (under “Extensions”).
Also under “Extentions”, enable Basic Constraints, change Key Usage, to set “Signature is proof of origin (nonrepudiation)” and under “Security” set the correct permissions for the earlier created user:
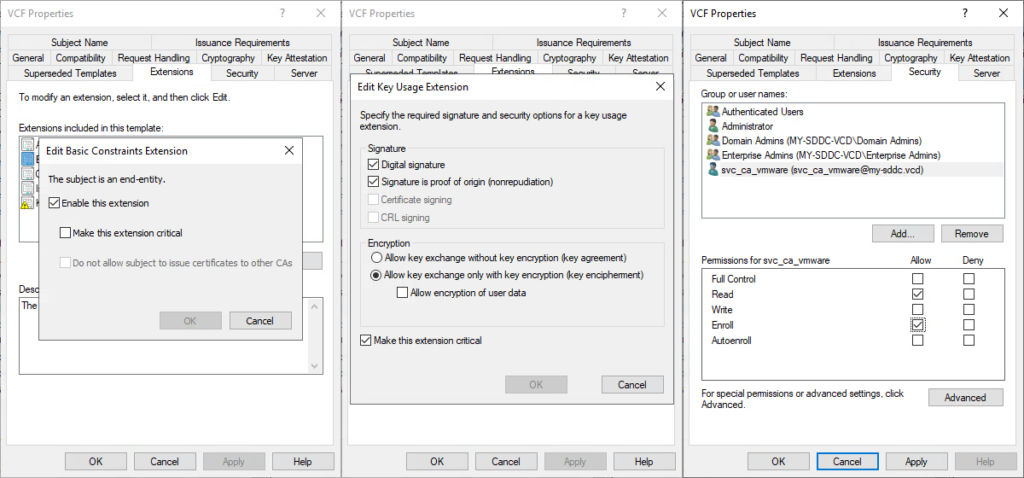
and save the changes.
After this, add the template to the CA (through certsrv.msc):
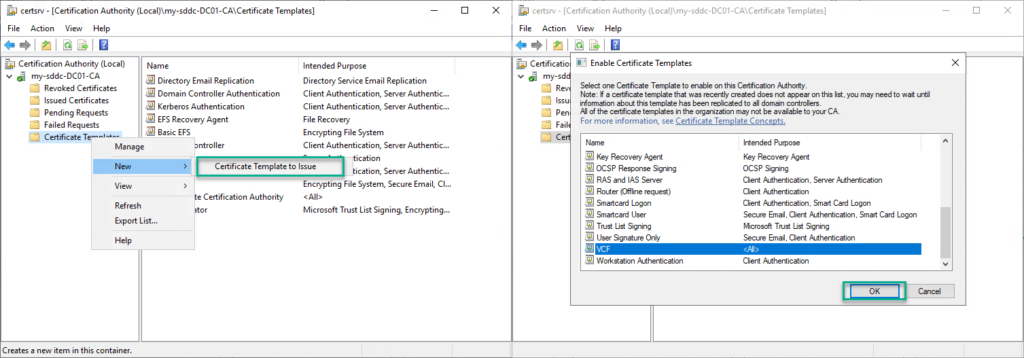
(see for more details: https://docs.vmware.com/en/VMware-Cloud-Foundation/4.5/vcf-admin/GUID-B83D4273-F280-4978-B8BD-63A283F803A9.html)
When this is all done, we can:
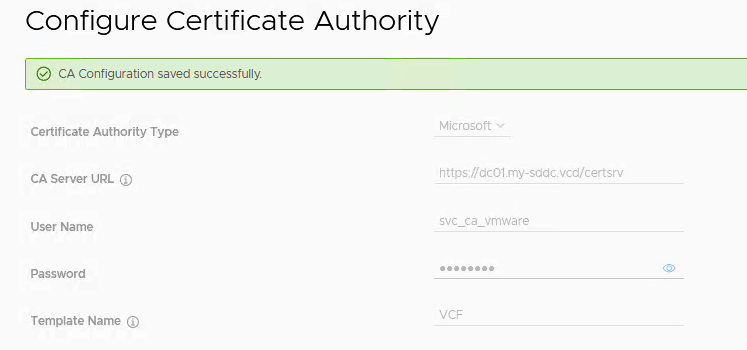
Configure the CA settings in VCF:

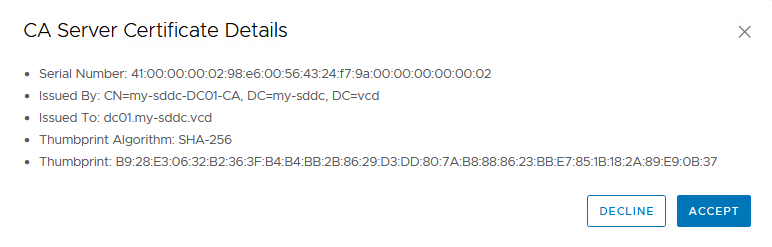
(don’t put an “/” after certsrv, that will result in an error saying “CA server url is invalid”) and validate that it works. We will see the CA Server Certificate Details for us to accept:
Last step is to configure the certificates for the VCF environment. First we head to the Management Domain. In there we go to the “Certificates” tab and select all the components for which we want to install Certificates:
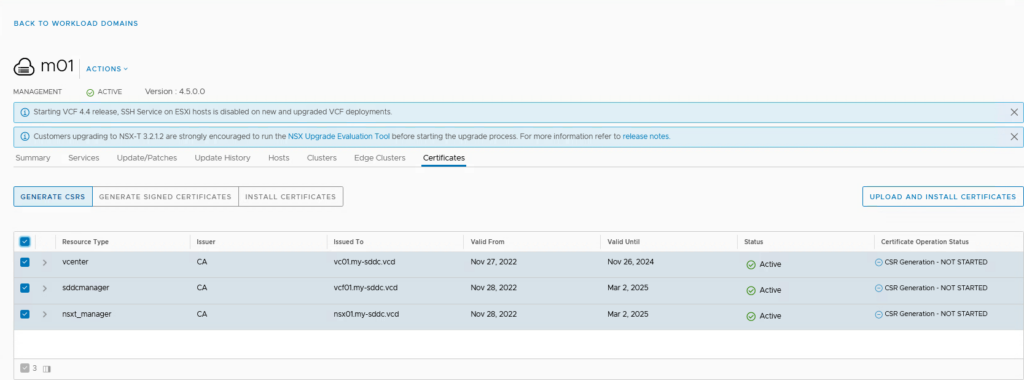
then click Generate CSRS (Certificate Signing RequestS):
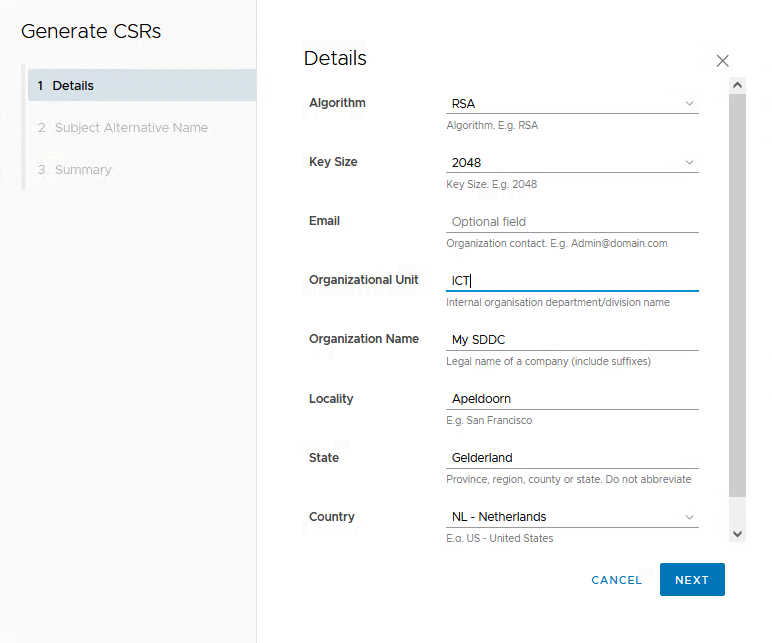
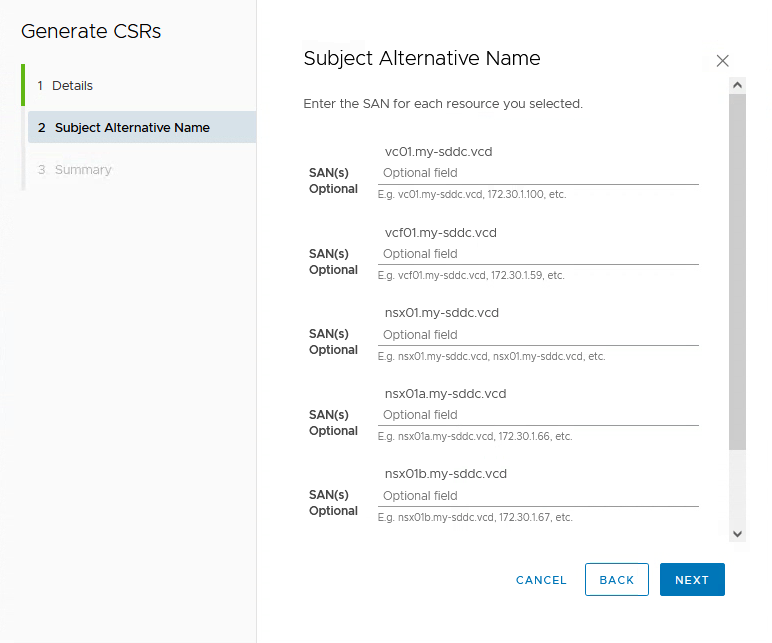
and fill out the form. Then click Next and any SAN (Subject Alternative Name) if needed:
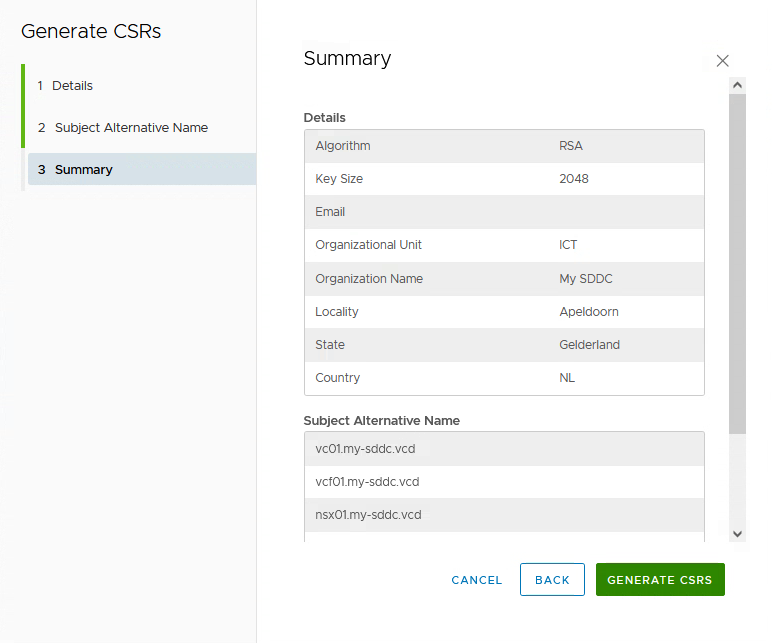
Review the Summary and click “Generate CSRS”:
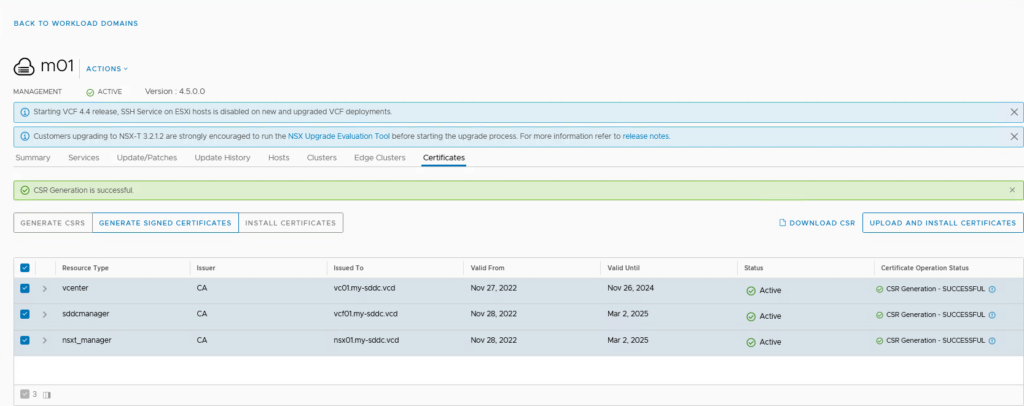
After this is done, the next step is to take these CSRS and create the Signed Certificates with them. Again, select all the relevant components and click “Generate Signed Certificates”. This will take the CSR for each of the components and have it signed by the CA that we have configured in the previous actions:
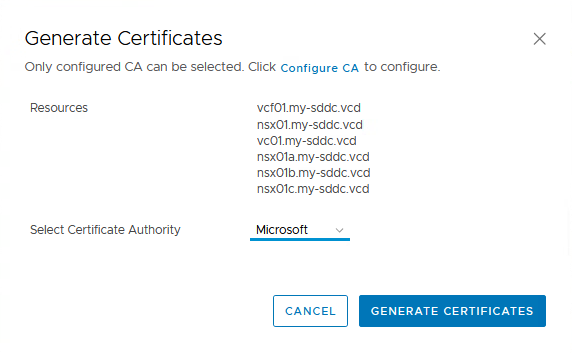
Select the correct CA and click “Generate Certificates”:
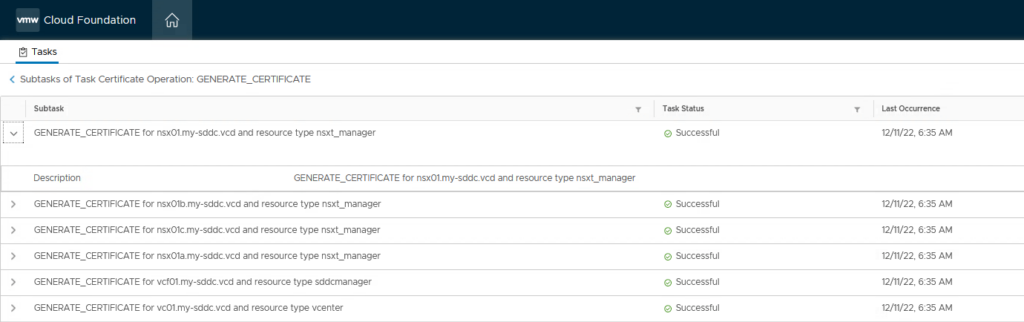
We can follow and review the Task in the Tasks window:
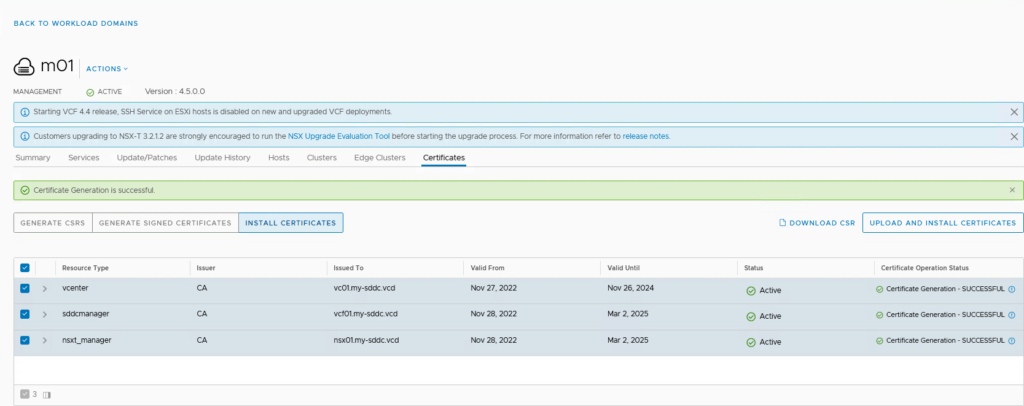
and after it finishes, the Certificates are ready to be installed:
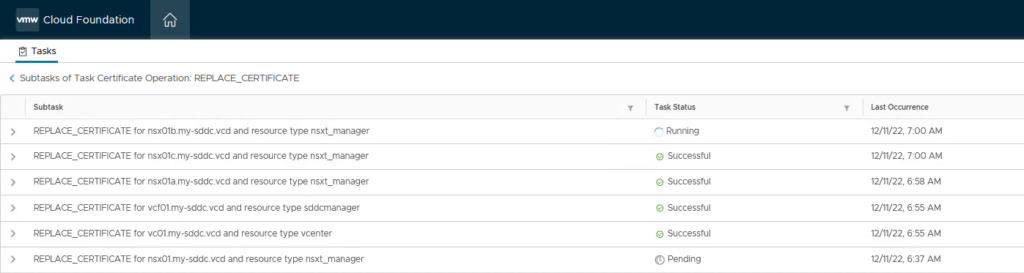
This also can be viewed in the tasks window (this will take some time, mostly because it will demand restarts of several services):
After the Management Domain is completely running on new certificates:
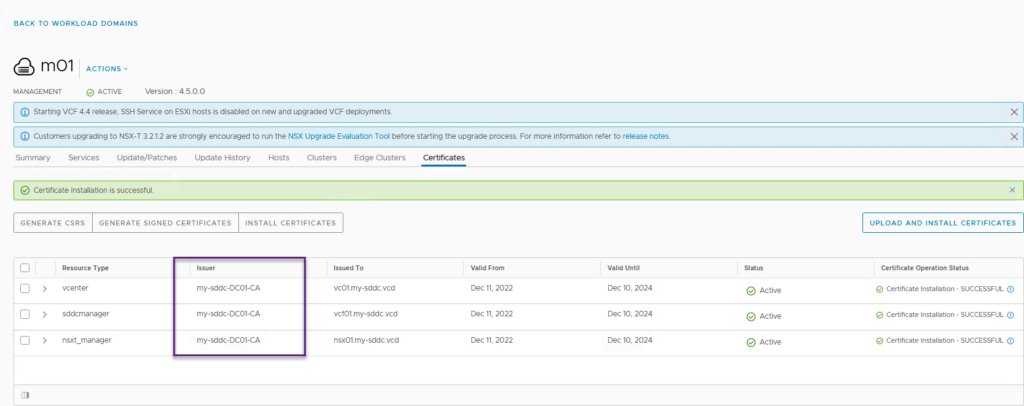
We can repeat these steps for the Workload Domain.
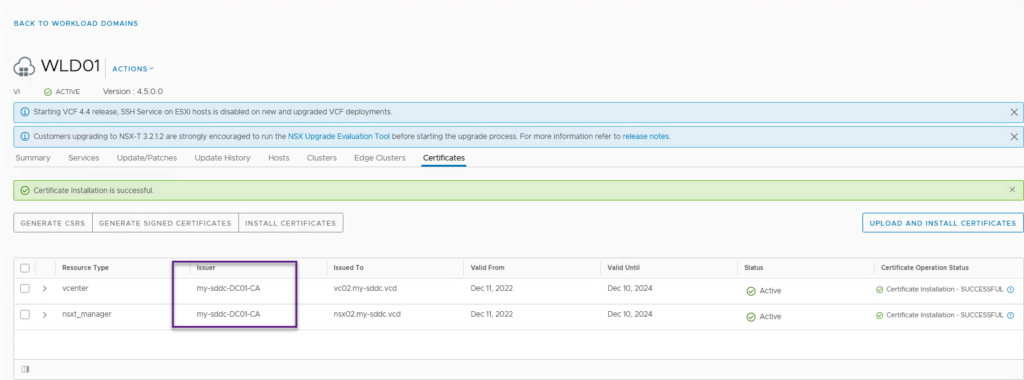
And we are done with installing our certificates. Next up, back-ups for SDDC Manager, NSX and vCenter Server
8 thoughts on “VCF on VCD: 2a – Certificates”