Adding a VPC with NAT on Flow Virtual Networking
A little while back, I created a non-NAT VPC, with BGP routing, to allow VM’s to be fully routed in my virtual environment. As I am now studying for the NCM-MCI exam, I wanted to look a little further in to FVN. First step here, is to create a new VPC, based on NAT. This is more or less the best practice, when doing VPC’s, so this shouldn’t be to difficult. No need for BGP and such…
So, the target environment, I am aiming for (completely parallel to the already existing one for VPC03), will be something like this:

So, I am starting with the configuration of the Subnet called “External-Uplink-VPC04-NAT”. This will be a new VLAN-ID (1004) with a new subnet: (172.30.4.0/24). This has already been created on the pfSense, including all NAT rules there, so I can reach the rest of the network, through the pfSense).
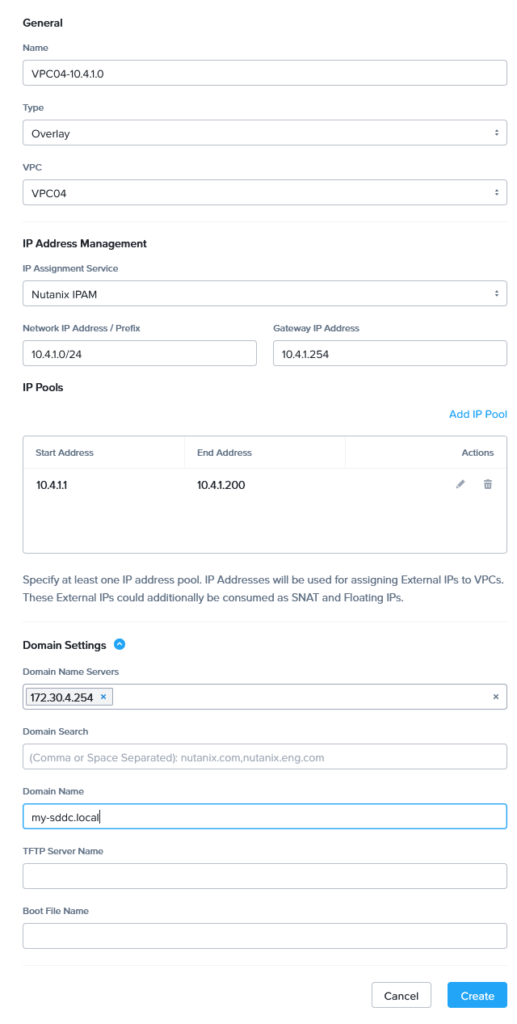
We create the new subnet (I had to change the name, see the end of this article):

Couple of things to note here:
- We enable the subnet for External Connectivity for VPCs.
- We use NAT
- We have defined the subnet and an IP-Pool.
- The IP-Pool can later be used for SNAT and for Floating IP Addresses (dedicatedly assigned to VM’s).
Next, we can create the VPC:
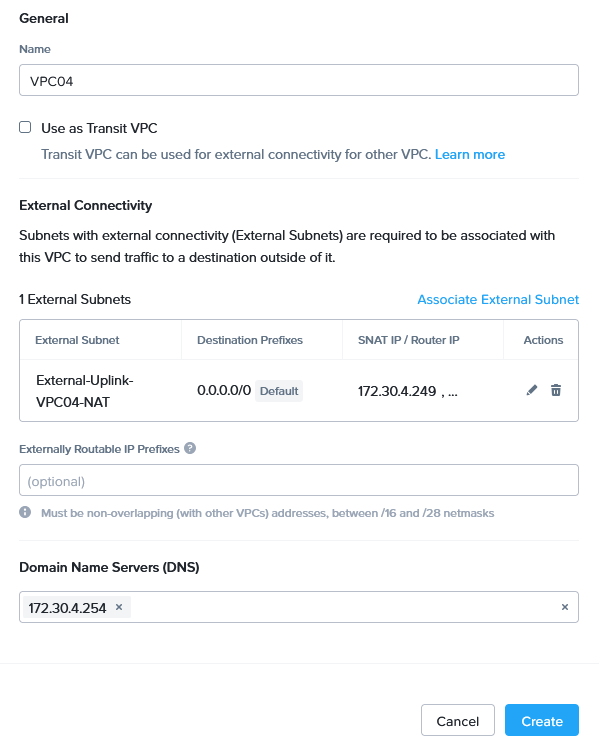
The External Subnet association is created as such:
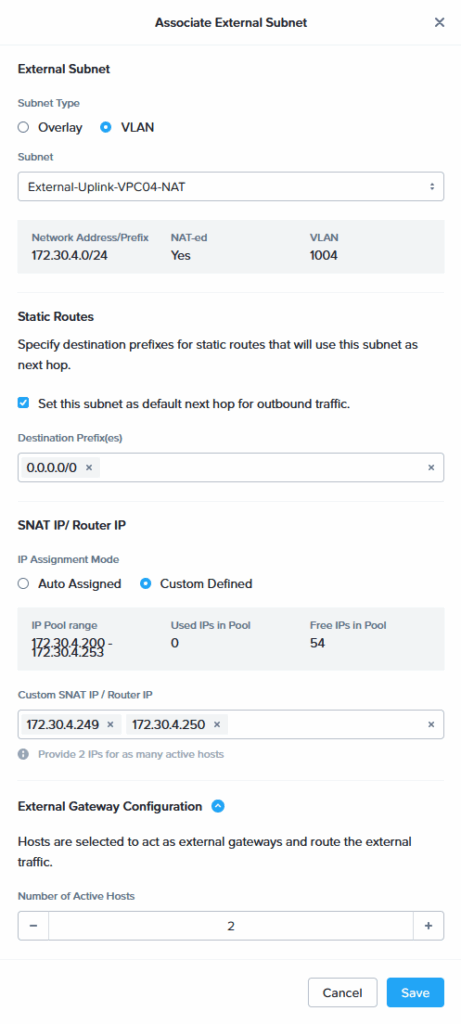
As with the creating of the non-NAT VPC, couple of things that are noteworthy here:
- We have selected the “Set this subnet as default next hop for outbound traffic”. This will enable all traffic that flows outside of the VPC to go over this VLAN. The external gateway is the one we have defined in the previous step, creating the subnet.
- We define two IP Addresses to be used for SNAT. We can control the amount of IP Addresses used for this, in the last field. These IP Addresses are assigned to hosts in the cluster.
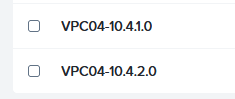
After the VPC has been created, we can create subnets. I will create two subnets (only one displayed here):
The end result:
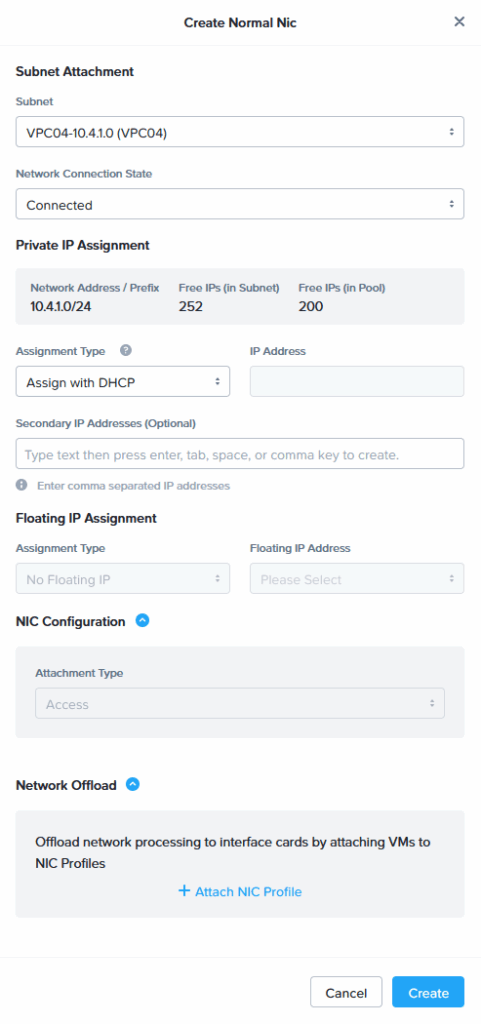
And these subnets will be used to connect the two VM’s two, that are shown in the initial picture. This does mean, removing the NIC and creating a new NIC attached to the new subnet:
(done for both VMs). After that, and starting the VMs:
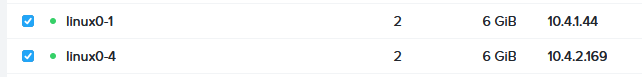
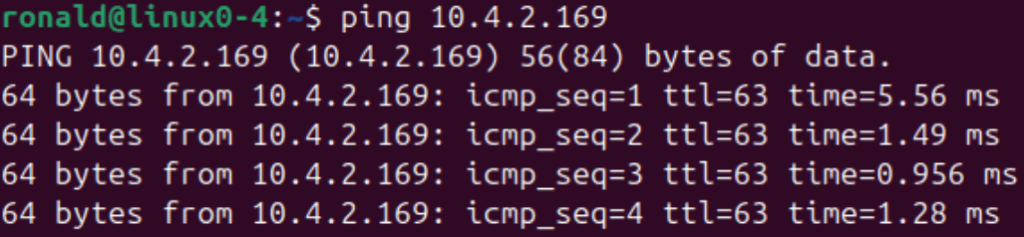
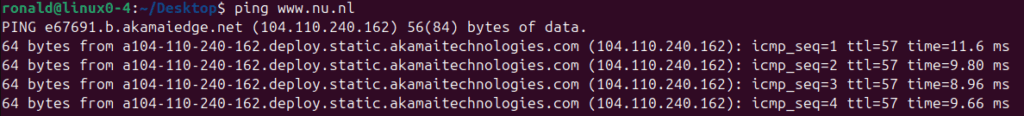
They can connect to each other:
and to the external (pfSense) network:
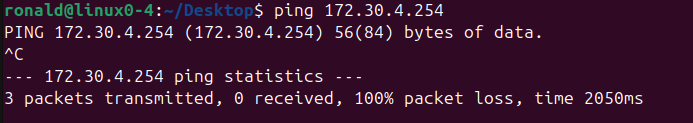
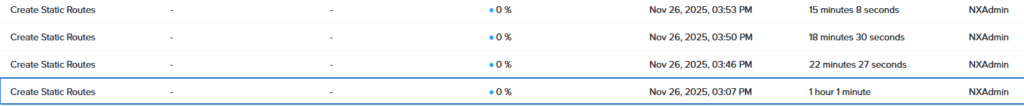
Failed. This seems to be related to the inability of my environment to create a static default route. I do see a couple of the tasks to do this. I double checked the connectivity and tried selecting “Set this subnet as default next hop for outbound traffic” a couple of times.
I also tried adding a static route to the VPC manually, in the GUI, but all I can see are running (and not completing) tasks, that try to enable the route:
So, I decided to see if I can add this route in a different way. As a learning experience, so to say. The way to manipulate the routing table within Flow Virtual Networking, is through the Prism Central VM, where we can start the “atlas_cli”. I have not found any public facing documents on how to exactly do what I did, but I did find some internal documents.
I am sure, if this problem occurs in a Production environment, the best way to handle this is, through a support ticket. Suffice it to say, for me it was a learning experience, so the ultimate result was:
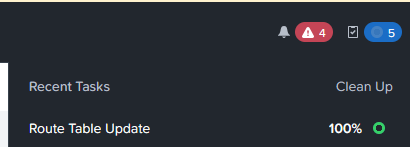
I did have to rename my subnet to get this working. Apparantly it had a problem with the Parenthesis ” ( )”, when adding the route through the CLI.
When I changed the name to “External-Uplink-VPC04-NAT”, the addition of the static route went through, on the cli. It does show in the GUI though:
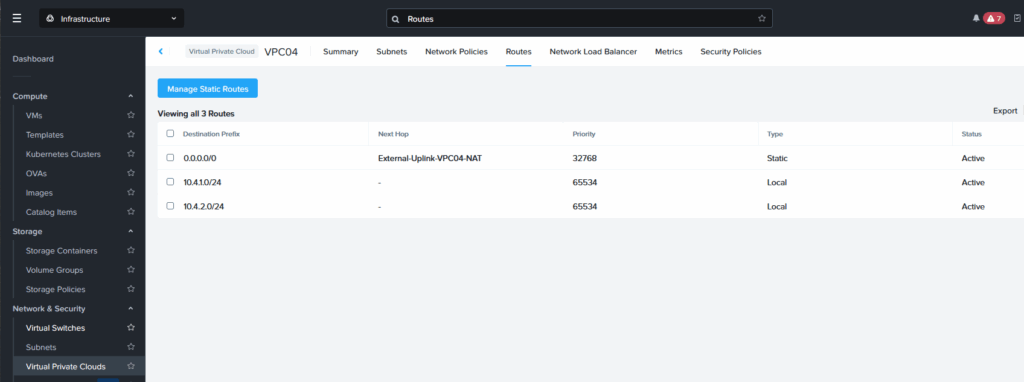
And the VM can find the pfSense:
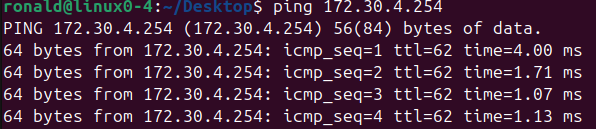
And the rest of the outside world:
Not exactly sure why creating the static route through the VPC creation or, after creating the VPC, through the GUI, didn’t work though. I didn’t run into this issue with VPC03, because there I use BGP as a routing protocol. These routes do get added to the VPC routing table.
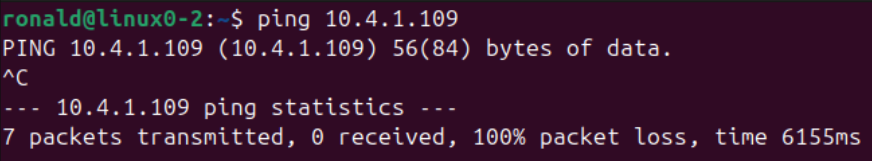
The VMs in the other VPC (VPC03) are also reachable, because that is a routed connection, with routes being distributed by BGP:

That means that a flow from a VM from VPC04 to VPC03, with NAT to No-NAT works. The other way around does not work, because VPC04 is connected through a NAT connections, which means that traffic will succesfully go out, but not in:
This is be a desired situation, since a VPC is meant to be a boundary. But if we did want to be able to communicate with one or two certain VMs within the VPC, we can use a “Floating IP Address”, that is part of the subnet which is used for the connectivity to the outside world (eg. 172.30.4.0/24).
The Floating IP addresses (FIPs) will be assigned from the IP Pool we created when we created the uplink subnet:

To create a new FIP, we go to “Floating IPs” under “Network & Security” and click on “Request Floating IP”:
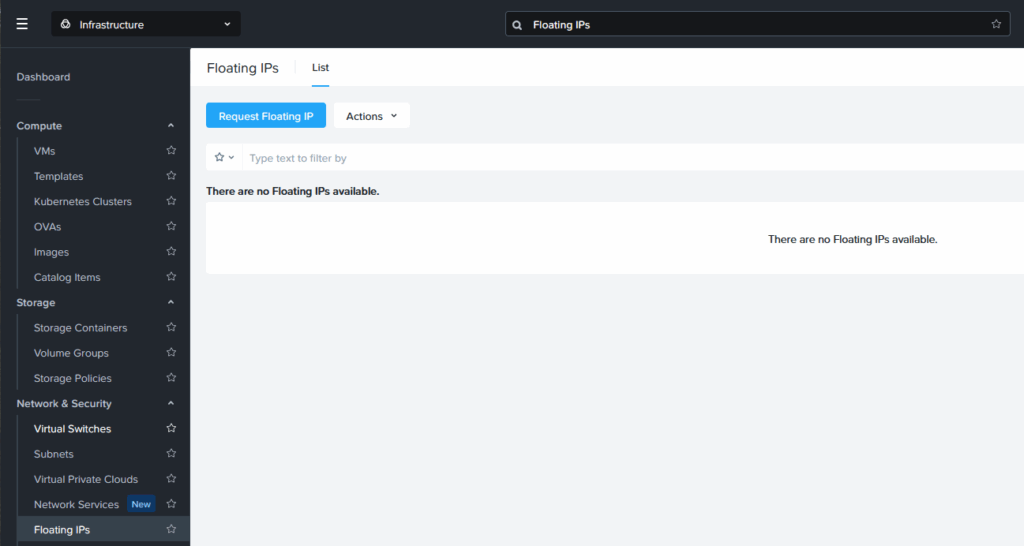
We select the External Subnet (only the NAT subnet is selectable here):

We fill out the number of FIPs we want, select the button to assign them to VMs and do so in the boxes beneath. We have also chosen to Define Custom Floating IPs. If we leave that open, the system will select the FIPs from the pool, but with it selected, we can choose which FIP is assigned to which VM.
After completing this, by clicking Save, we can see:

And, from the VPC03 VM, we can now reach the VPC04 VMs, by using their FIP:

So the end result of this exercise, is the following virtual network environment, including VPC03:
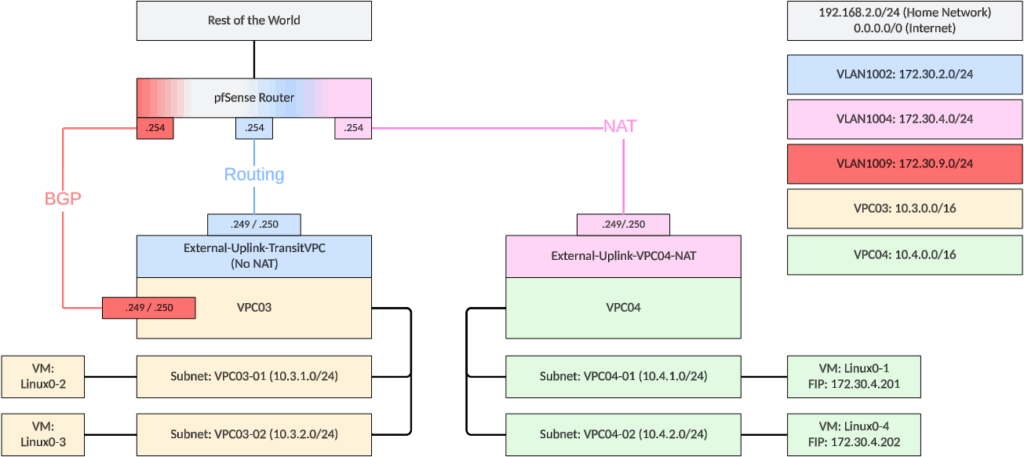
The next step, in my virtual networking explorations, will be looking at multiple (routed) VPC’s, through a Transit VPC.
One thought on “Adding a VPC with NAT on Flow Virtual Networking”